
Having the right suppliers, vendors, partners, affiliates, and other kinds of third parties is critical to your organization’s success. But third-party risk management (TPRM) professionals also recognize the potential risks associated with poorly vetted and managed third parties, such as:
Therefore, there’s no question that a good third-party risk management program is important. But even though it is business critical, many organizations still lack the resources (financial, human, and organizational) to deliver and support a successful program. Recent benchmarking research across more than 300 TPRM professionals reveals:
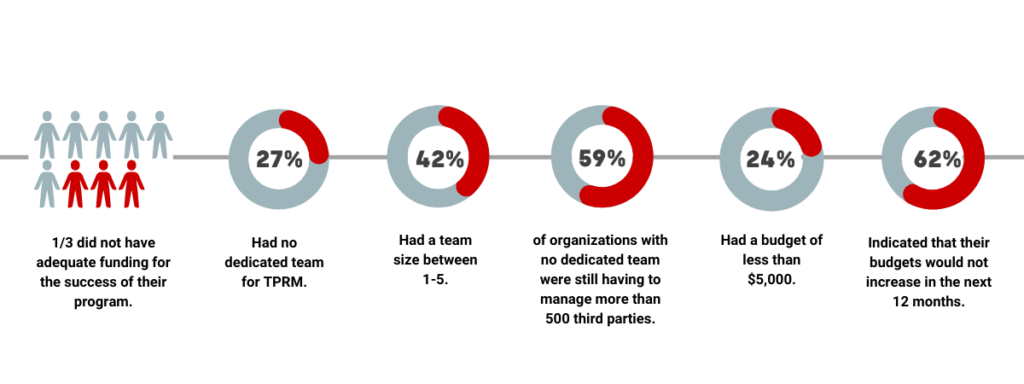
These insights are despite an expectation by regulators that programs are properly resourced. For example, the U.S. Department of Justice Criminal Division’s Evaluation of Corporate Compliance Programs guides its examiners to ask: “Is the Corporation’s Compliance Program Adequately Resourced and Empowered to Function Effectively?” Proper resourcing should not be neglected, and TPRM professionals should champion investment cases to senior management to ensure they are not exposed here.
But this does mean that teams still need to do a lot with a little. How can you make your resource go further?
Thankfully, there’s various ways you can make your resources go further, by ensuring your TPRM tools work smarter.
Better automation is a critical component of any third-party risk management program. It makes no sense to have scarce, and (often) expensive resources managing tasks and processes that could be automated. It’s inefficient, and means that the more important stuff (like actually understanding and managing risks) can get left behind. At the heart of better automation is business workflow management.
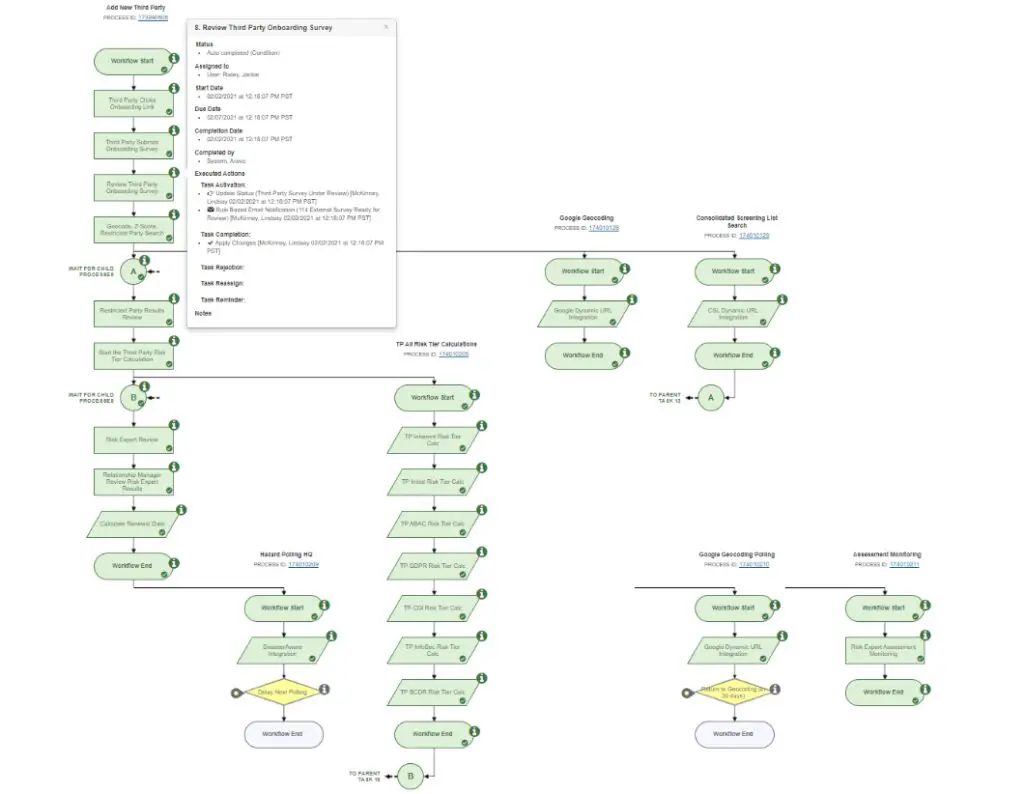
Smarter automation is key here. Your system should automate as much of the process for you as possible – including triggering actions, routing, notifications, communications, scoring inherent risk, risk tiering, calling the relevant risk intelligence from API integrations (such as cybersecurity ratings, sanctions screening, hazard tracking and geolocation data) and triggering escalations. This allows for much of the heavy-lifting to already be done for you, ensuring that you can focus on the more strategic elements of your program.
You want these workflows to be visual (so you can easily track where third parties are in the automated processes), conditional, and able to manage complex parent-child workflows. Configuration changes to these workflows should ideally be drag-and-drop, and cascaded through the workflows of the system. An example of a workflow in the Aravo system, which brings this to life, is below. Embedded in the workflow is additional audit trail information that you can see at a glance.
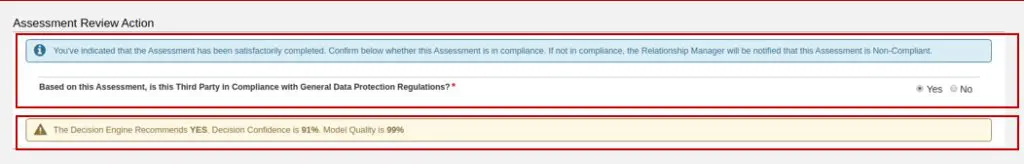
AI and machine learning, done properly in a TPRM system, becomes another, smarter level of automation. It’s also not as scary as it can sound – you can train it on your own data (the decisions your risk experts have made) so it takes into account the risk tolerances of your organization. There’s a variety of use-cases for AI which are explained in this white paper, but an easy one to implement is decision support, whereby the system can make a suggestion (based on its intelligence) and provide a level of confidence on that decision. This helps busy, time-constrained teams become more efficient. All these actions will also be captured in your workflow and audit trail.
Teams are much more efficient when their tools work for them (and simplify processes and analyses rather than complicate them). The system that you use for TPRM should not exist in a silo (nor create one). Your tools should ‘work better together’.
Integration
Better data means better business decisions – your system should make it easy to govern, integrate, and enrich your data from internal and external sources. Look for:
Smarter scoring
Your TPRM system is much like a trusted member of the team – and you want that team member to be both smart (a math whiz) and fast. It should incorporate a mathematical evaluation engine – with built in risk scoring models, such as inherent risk scoring and other models such as Altman-Z scoring (for assessing the financial stability of vendors). Scoring should be configurable (as different organizations have different risk thresholds).
Cross functional
TPRM is a team effort, and you want that team on the same playing field. Ideally, the different functions across your organization should not be using disparate systems and processes for managing third-party risk. With that in mind, your solution should provide a collaborative platform for all functions involved in the TPRM process including: procurement, risk, compliance, legal, privacy, audit, senior management, business users and third-party users. Different processes can be automatically routed to them, they can communicate with each other within the system, and they benefit from their own role-based dashboards and reporting – highlighting the information that’s important to them.
Holistic
Your system should help your team take a holistic approach to TPRM. It’s not efficient to manage different kinds of risks associated with your third parties, or manage different parts of the third-party lifecycle in different systems.
Transparent
Your system should also be a great ‘communicator’. The information it serves up in the form of dashboards, visualizations and reports will be meaningful, and appropriate to the team member interacting with it. It should also keep a comprehensive and accessible audit trail and history.
Finally, pre-configured/pre-packaged solutions can take a lot of the heavy-lifting out of standing up a TPRM program. They can usually be implemented quicker than solutions that are highly customized and be ready to use right away. Implementing a ready-to-use application should be simple and easy to set up with modest teams and experience.
In addition to decreasing time-to-value, pre-configured solutions allow you accelerate your program maturity by taking advantage of the expertise of the TPRM vendor. An experienced vendor will combine their first-hand knowledge of best practices for the industry and the risk domain(s) you’re assessing with external guidance from regulators, professional organizations, and standards boards.
A well-designed, pre-configured solution is also helpful when the subject matter expertise of your team is still developing. For instance, let’s say your team is asked to augment your current third-party review process with anti-bribery/corruption due diligence, an area in which you currently have no SME. Being able to rely on assessments that have been purpose-built to align with regulatory and other guidance lets you quickly and confidently launch a program without scrambling to identify the proper questions, screening tools, and risk scoring on your own.
To sum it up, in an environment where human capital can be scarce, the right technology can ensure that you work smarter and not harder as you manage your third-party risks. To see smarter technology in action – schedule a demo today.
Share with Your Friends: